Part 1 of 3 in the "1984 → 2048: Europe's Choice" trilogy
You're reading this on a telescreen.
It knows your location. It knows who you messaged this morning. It knows what you searched for last night when you couldn't sleep. It has photographed your face dozens of times today and transmitted the data to servers you'll never see, in countries whose laws don't protect you.
You paid good money for it. You feel naked without it.
George Orwell imagined the telescreen as a nightmare imposed by the state. He never imagined we'd buy them willingly, carry them everywhere, and feel anxious when they're not in reach.
"The world is divided into three great super-states: Oceania, Eurasia, and Eastasia. They are perpetually at war with each other in shifting alliances. The war is not meant to be won—it is meant to be continuous."
— George Orwell, 1984 (1949)
Three empires are fighting for control of the digital world, and Europe is the territory they're carving up between them. America takes your data through platforms you use daily. China manufactures the devices in your pocket. Russia poisons your information environment. All three treat you as a resource to be extracted, not a citizen to be protected.
Europe could resist. It has 450 million people and a €17 trillion economy. Instead, it's scrolling.
This is the first of three articles examining Europe's choice through Orwell's lens. Here we map the superstates. Part 2 examines how Europe is being targeted. Part 3 explores whether a fourth way exists.
The three digital superstates
Oceania 2.0: the American surveillance model
In 1984, Oceania's ideology is "Ingsoc" (English Socialism), a regime that promises freedom while delivering total control. The Party's slogan, "Freedom is Slavery," captures the contradiction at the heart of its power.
In 2026, America's ideology has a different name: surveillance capitalism.
Harvard professor Shoshana Zuboff defines it as "the unilateral claiming of private human experience as free raw material for translation into behavioral data." These data are then packaged as prediction products and sold to advertisers, political campaigns, and anyone willing to pay for insight into what you will do next.
The business model is elegant in its extraction: users generate data, companies collect it, algorithms process it, and predictive models sell it to third parties. Google, Facebook, Amazon, Apple—the platforms Americans use daily—run on this logic. The service is "free." You are the product.
The NSA connection
But surveillance capitalism is only half the American model. The other half wears a government badge.
The PRISM program, revealed by Edward Snowden in 2013, showed that the NSA obtained electronic communications in real-time from internet service providers including Microsoft, Yahoo, Google, Facebook, Skype, YouTube, and Apple. The Foreign Intelligence Surveillance Court found that PRISM accounts for 91% of the roughly 250 million internet communications acquired each year under Section 702.
The program didn't end with Snowden's revelations. PRISM targets have grown steadily: from 89,138 in 2013 to 291,824 in 2024. In 2024, just two days after Congress renewed and expanded Section 702, the FBI's deputy director sent an email imploring agents to "use" the surveillance authority.
This is the Oceania model updated for the digital age: corporate extraction plus government access. Silicon Valley builds the infrastructure. The NSA taps it. The CLOUD Act ensures that American law reaches any data stored by American companies, anywhere in the world.
The Party in 1984 watched through telescreens. America watches through platforms you downloaded voluntarily and hardware you purchased with your own money. Oceania's slogan was "Freedom is Slavery." The 2026 version: "Convenience is Surveillance."

Eurasia 2.0: the Russian-Chinese axis
In 1984, Eurasia spans the Eurasian landmass from Portugal to the Bering Strait: a vast authoritarian bloc where the state controls all.
In 2026, this bloc is forming again. On February 4, 2022, just weeks before Russia invaded Ukraine, Xi Jinping and Vladimir Putin announced a partnership with "no limits" and no "forbidden areas of cooperation."
The "no limits" partnership
This was not diplomatic theater. In May 2025, China and Russia deepened their partnership further, signing deals spanning investment, trade, energy, space, and culture. Presidents Xi and Putin publicly rejected the U.S.-led world order and articulated a new vision with Beijing and Moscow at the center.
The partnership is asymmetric (China is the senior partner) but functionally integrated:
- Technology transfer: Chinese defense universities have significantly increased research partnerships with Russian institutions since 2019, providing Moscow access to strategic technologies cut off by Western sanctions, particularly aeronautics and drone technology.
- Sanctions evasion: China supplies Russia with dual-use industrial inputs including microelectronics, military optics, drone engines, and satellite technology. Nearly 90% of Russian-Chinese transactions are now settled in yuan and rubles.
- Military coordination: Joint exercises, shared submarine technologies, and collaborative AI and quantum computing research create an integrated defense posture.
China's surveillance industrial complex
But the partnership extends beyond military hardware. China has built what Stanford researchers call a "surveillance industrial complex", and it's for export.
Through companies like Huawei, Hikvision, Dahua, and CloudWalk, China has exported its "smart city" surveillance products to over 80 countries. Many are Belt and Road Initiative participants. The technology includes facial recognition, video analytics, mobile tracking, and data fusion capabilities.
The numbers tell the story:
- Huawei has built approximately 70% of Africa's 4G networks
- 266 Chinese technological initiatives operate across Africa, from data centers to smart cities to surveillance networks
- Research across 90 countries found Chinese companies exporting AI surveillance to at least 54
The research is damning: in autocracies, Huawei technology facilitates digital repression. CloudWalk's facial recognition database in Zimbabwe is reportedly used to monitor government critics. Huawei technicians have been caught engaging in political espionage in Uganda and Zambia.

Russia's information warfare machine
Russia brings a different capability to the partnership: information warfare at scale. While China exports surveillance hardware, Russia exports chaos.
The Internet Research Agency, the disinformation campaigns documented in the Mueller Report, the operations targeting Brexit and European elections: these are not aberrations. They are doctrine. The Gerasimov Doctrine explicitly describes how information warfare can achieve objectives that conventional military force cannot.
In Orwell's novel, Eurasia and Eastasia are sometimes allies, sometimes enemies, but functionally identical in their totalitarianism. In 2026, Russia and China present different flavors of the same control model: surveillance hardware from Beijing, information warfare from Moscow, merged into a single authoritarian tech stack.
Why China + Russia = one digital faction
Orwell collapsed Eurasia and Eastasia into interchangeable enemies because their systems were functionally identical. Despite cultural and historical differences, both served the same purpose: total state control over their populations.
The same logic applies today. Despite tensions and asymmetries, China and Russia have converged on a shared digital model:
| Capability | China | Russia | Combined Effect |
|---|---|---|---|
| Surveillance tech | World leader in facial recognition, smart cities | Limited domestic, imports from China | Global export of authoritarian infrastructure |
| Information warfare | State media, censorship | Troll farms, disinformation campaigns | Coordinated attacks on Western democracies |
| Internet model | Great Firewall, total control | RuNet, increasing isolation | Sovereign internet as template for authoritarians |
| Tech standards | Alternative to Western systems | Adoption of Chinese systems | Parallel digital ecosystem outside Western control |
The February 2022 "no limits" declaration was not the beginning of this convergence, it was its public acknowledgment. The partnership predates the Ukraine invasion, will survive it, and serves both regimes' core interest: demonstrating that authoritarianism can coexist with technological modernity.
This is the Eurasia of 2026: not a single monolithic state, but a coalition of authoritarian digital models united against liberal democracy.
The perpetual digital war
"We have always been at cyber war with..."
One of Orwell's sharpest insights: the war between superstates is not meant to be won. It is meant to be continuous.
"The war is waged by each ruling group against its own subjects, and the object of the war is not to make or prevent conquests of territory, but to keep the structure of society intact."
The superstates periodically switch alliances (Oceania was always at war with Eastasia; Oceania was always at war with Eurasia) but the war itself never ends. Its purpose is not victory but perpetuation.
The digital war has no armistice
Cyber conflict follows the same logic. There is no peace treaty to sign, no territory to exchange, no moment when the war concludes.
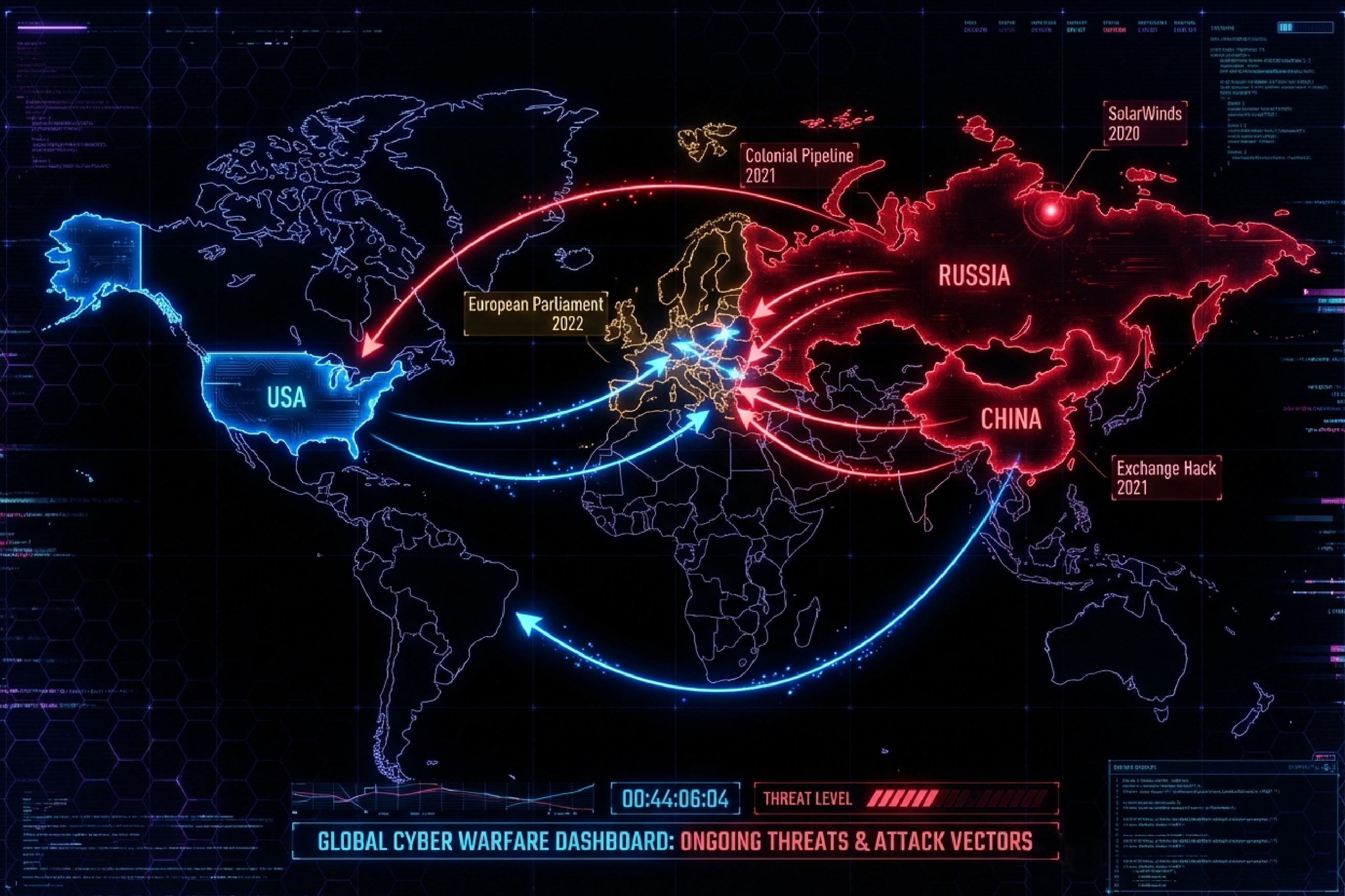
SolarWinds wasn't a hack. It was an occupation. Russian intelligence lived inside 18,000 organizations for months, reading their emails, watching their decisions, copying their secrets. The U.S. Treasury, Commerce Department, Homeland Security: all compromised. The intruders left when they chose to, not when they were caught.
Microsoft Exchange (2021): Chinese hackers exploited vulnerabilities in hundreds of thousands of email servers worldwide. Your company probably ran Exchange. Colonial Pipeline (2021): Russian ransomware shut down fuel to the U.S. East Coast. European Parliament (2022): Attacked during a debate on Russian state terrorism, a message delivered in real time. German government (2023, 2024, 2025): Repeated intrusions, attributed to Russian and Chinese actors, that Berlin can document but cannot stop.
The attacks are continuous. The attribution is murky. The responses are inadequate. This is not a bug in the system—it is the system.
The real enemy: their own citizens
Orwell understood that external war serves internal control. The Party needs Eurasia and Eastasia as enemies not to conquer them, but to justify monitoring its own population.
America's security ratchet
After 9/11, the United States built a surveillance apparatus justified by the war on terror. The Patriot Act. PRISM. Section 702. Each crisis expanded state power; none contracted it when the crisis passed.
The NSA collects 250 million internet communications annually under Section 702: communications of foreigners, yes, but also Americans caught in the dragnet. The justification is always the same: we need this power to keep you safe from external threats.
China's social control
China makes the connection explicit. The social credit system, the 200 million surveillance cameras, the Great Firewall: all justified as necessary for stability and security. External threats (American containment, Taiwanese independence, Uyghur terrorism) provide the rationale for internal control.
Russia's sovereign internet
Russia's RuNet project aims to create a fully controllable domestic internet, capable of disconnecting from the global network. The justification: defense against Western cyber attacks. The effect: total control over information available to Russian citizens.
The pattern is universal
Each superstate tells its citizens: We must monitor you to protect you from them. The external enemy justifies the internal surveillance. The war, whether against terrorism, Western influence, or Eastern authoritarianism, is the excuse for the telescreen.
In 1984, the telescreens watched everyone, always. In 2026, the smartphones do the same. And we pay for the privilege.
The superstates need each other as enemies more than they need to defeat each other. American surveillance requires Russian hackers as justification. Chinese control requires American containment as excuse. Russian repression requires NATO expansion as rationale. The perpetual war keeps all three systems intact.
The map is drawn. Three digital superstates, each watching their citizens, each pointing to the others as justification.
But look again at Orwell's map. Notice what's missing.
In Orwell's geopolitical vision, Europe doesn't exist. Britain has been absorbed into Oceania. Continental Europe has been swallowed by Eurasia. The civilization that gave the world the Enlightenment, human rights, and democratic governance has been erased, divided between rival empires.
This is not fiction. This is the trajectory.
In Part 2: Europe Under Siege, we examine how the superstates are already working to absorb Europe—through troll farms and bank transfers, through compromised politicians and captured platforms. The siege is not coming. It has begun.
450 million people. €17 trillion in GDP. A market large enough to set global standards. All of it dependent on American platforms, Chinese hardware, and vulnerable to Russian information warfare.

The clock is striking thirteen. Can you hear it over the notification pings?
Series context
Position: Part 1 of 3 in "1984 → 2048: Europe's Choice" trilogy
Previous: —
Next: 1984 → 2048: Europe Under Siege (Part 2)
